Team!
Happy Thursday! Tonight, I want to write about a topic that I haven’t seen a lot of information circulating about it, but it probably should be. Now more than ever information security is in the forefront of everyone’s mind after the unprecedented breach of SolarWinds and other parties. The timeline and scale of this attack alone were monumental, and that’s describing it without even getting into any of the intricate details surrounding it.
‘T’ Stands for Trusted
If you are familiar with HPe’s product line, you probably already know that they had models in the ProLiant DL family called DL-whatever-e and DL-whatever-p, e.g. DL380p. The ‘e’ stood for Entry Level model and the ‘p’ was the Performance model, and the hardware that was packed inside reflected the unit that you purchased. Recently, with the ProLiant Gen10s HPe announced that they are releasing the DL-whatever-T, where the ‘T’ stands for Trusted.
What’s the difference?
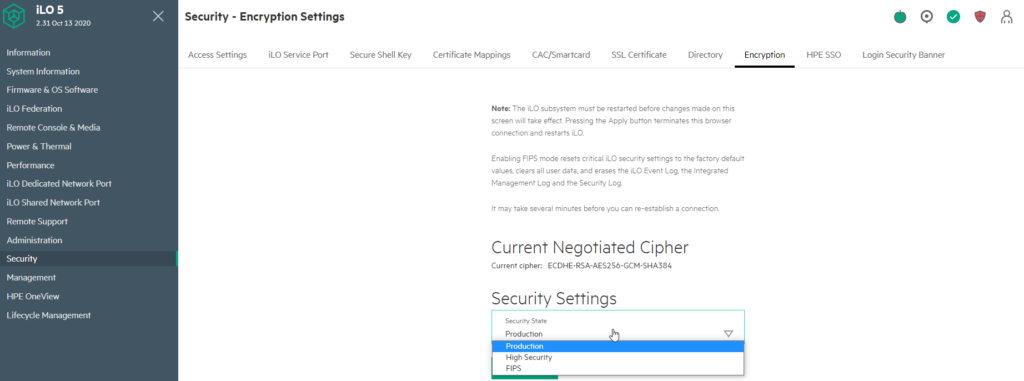
HPe has truly stepped up their game in the security arena with the announcement of this new initiative. They take steps to ensure that the security of your infrastructure begins where it should have begun long ago, at the supply chain. There has always been a mountain of opportunity for tampering at the manufacturer level. You read articles all the time about cell phones and other hardware leaving the factory and making their way into the consumers’ possession with malware already on them. Now this doesn’t necessarily mean that it was tampered with at the factory, but it also doesn’t rule it out by any means. So how do we protect against this? Well, HPe has come up with a plan to try to prevent this from occurring. When you buy a typical server from HPe the server is shipped in Production mode. With the T-series, the server is placed into High Security mode at the factory. The difference is that High Security makes use of the same cipher suites that FIPS does (though it doesn’t follow the same initialization procedures). It also enforces more stringent security policies requiring authentication to use the host-based utilities such as ROM Based Setup Utility (RBSU).
If HPe is loading OSes for you at the factory, they will enable UEFI Secure Boot with the T-series models. This helps prevent the OS from being tampered with prior to the server’s arrival at your facility. The Server Configuration Lock is something that is exclusive to HPe and, in my opinion, a phenomenal idea to prevent unauthorized modifications prior to delivery. It logs the server’s configuration to the server itself. If anything was tampered with or changed the customer will receive an alert at boot warning them of the changes. The Configuration Lock has a password that is generated at the factory and only distributed to the end customer to use to unlock the server once it arrives. Intrusion detection switches have been around for some time, and seemingly disappeared from the “general population” of servers. HPe is bringing them back in the T-series. If the server is opened enough to trigger the switch an event gets logged in iLO, even if the server is not powered. Finally, if required, HPe can provide delivery and/or installation services by verified companies to help take away the possibility of the unit being tampered with while en route to its destination. All these extra steps and features will help protect you from the factory to the datacenter rack. Couple this with HPe’s Silicon Root of Trust and you can consider your infrastructure that much more secured. Plus, it comes with a cool new sticker on it indicating it’s a T-series.

In my opinion, this is a game changer in terms of security. Sure, you could easily put iLO in High Security mode and install a little intrusion detection switch yourself, but how do you know that your server wasn’t infected before it was even put into its original packaging? You don’t, but these T-series servers will help you sleep a little better at night, or at least help mute the thought of it occurring at the factory level.
Thanks for reading. If you enjoyed the post make sure you check us out at dirmann.tech and follow us on LinkedIn, Twitter, Instagram, and Facebook!

Paul Dirmann (vExpert PRO*, vExpert***, VCIX-DCV, VCAP-DCV Design, VCAP-DCV Deploy, VCP-DCV, VCA-DBT, C|EH, MCSA, MCTS, MCP, CIOS, Network+, A+) is the owner and current Lead Consultant at Dirmann Technology Consultants. A technology evangelist, Dirmann has held both leadership positions, as well as technical ones architecting and engineering solutions for multiple multi-million dollar enterprises. While knowledgeable in the majority of the facets involved in the information technology realm, Dirmann honed his expertise in VMware’s line of solutions with a primary focus in hyper-converged infrastructure (HCI) and software-defined data centers (SDDC), server infrastructure, and automation. Read more about Paul Dirmann here, or visit his LinkedIn profile.
